enclaive
In a data-driven world, many innovation projects fail due to one crucial hurdle: protecting sensitive information during active processing. While data “at rest” and “in transit” can be reliably encrypted, the third dimension – data in use – has been a major vulnerability, especially in the cloud.
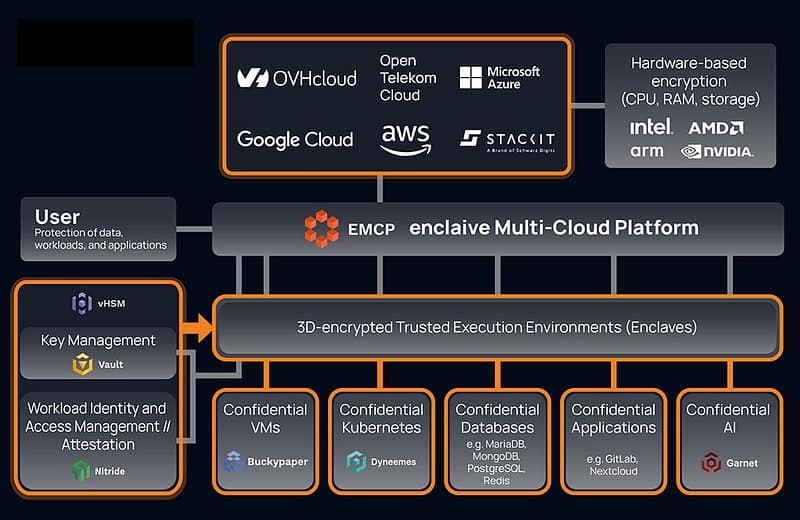
enclaive solves this problem with confidential computing and its “3D encryption.” This new security approach protects data even during processing in hardware-based, isolated trusted execution environments, also known as enclaves. Applications, databases, and AI workloads are thereby protected from unauthorized access, even by privileged administrators or the infrastructure provider.
Your benefits with enclaive:
- Easy integration into multi-cloud environments: Using the enclaive Multi-Cloud Platform (eMCP), enclaves can be set up and managed across multiple cloud providers with just a few clicks. enclaive’s technology is based on open source and common APIs (PKCS#11, KMIP, REST), and can therefore be integrated into existing infrastructure without any code changes.
- Sovereignty through key management: With its innovative vHSM (virtual hardware security module), enclaive offers a cloud-native and crypto-agile encryption module with hardware-level security. Building on the vHSM technology, enclaive’s Vault offers an independent key management system (Hold Your Own Key) in which all cryptographic processes and keys are secured in enclaves.
- Technically verifiable compliance: With Nitride, enclaive offers a second vHSM solution. The highlight: Using cryptographic attestation, Nitride ensures that enclaves only boot with verified, trusted components. This gives you verifiable integrity for confidential workloads and makes it easy to meet compliance and audit requirements.
- Ready for the post-quantum era: enclaive enables the encryption of data and applications in post-quantum-secure VMs (Buckypaper) and Kubernetes clusters (Dyneemes). This means that companies are already prepared for the era of quantum computers and can protect themselves against today’s widespread “harvest now, decrypt later” attacks.
- Confidential AI: You can also run their own AI models inside enclaves. In addition, enclaive offers Garnet, a GenAI firewall that filters and pseudonymizes sensitive data before interacting with external models. This makes it easy to comply with data protection regulations and protect intellectual property.
- Additional Use Cases:
- Protected Lift-and-Shift-Migrations
- Confidential Databases
- Confidential collaborations between different organisations
Find out more about enclaive
DataStore and enclaive have joined forces to offer:
- Comprehensive technical and sales support
- Joint marketing and lead generation initiatives
- Attractive and forward-looking product portfolio
- Solution Center for live demonstrations, training sessions, and proof-of-concepts
Discover enclaive:
Do you have questions? Here you can contact us:
Events
Events again soon.